Email is asking users to trust it every time they open a message. Do you believe an email comes from who it appears to come from? For many people, it could be an easy yes, but it’s surprisingly easy to fake an email and make it seem like it’s coming from a trusted source.
The people who first created the Internet didn’t include a way for people to verify the sender’s identity. Instead, when setting up email’s basic protocols, they balanced costs in computing power, implementation, and ease of use versus the risk of fraud.
They never imagined that 3.4 billion phishing emails would be sent every day. They didn’t include any authentication provisions for email to protect against phishing attacks, spam, or malware.
That’s where email authentication comes in.
What is email authentication?
Email authentication is the modern fix to this fundamental flaw. By implementing email authentication, you can ensure that anyone — an employee, customer, partner, or prospect — who receives an email that purports to be from your company can determine if the email is legitimate and, if not, flag or discard it.
You can get complete visibility and control over who sends email in your name. The importance of this has grown dramatically with the rapid growth in cloud services, over 10,000 of which send email on behalf of their customers for sales, marketing, customer support, HR, accounting, legal, and many other services.
By enforcing authentication and only enabling senders you authorize, you can block everyone else who attempts to send in your name – spammers, phishers, and even “shadow email” senders that may be legitimate but have not been vetted or authorized.
Email authentication standards enable any mail server to verify that an email with your domain in the “From:” address has been authorized to send in your name. Before it delivers a message to a recipient’s inbox, a mail server can check the following:
- Does the server sending this have the right to use the domain name (or names) listed in the message’s headers?
- If there’s a cryptographic signature attached to the message, does it match the public key on file for the domain it appears to be from?
- And do the headers match one another? (For instance, are the From: and Reply-to: fields the same?)
Email authentication methods
Email authentication is based entirely on open Internet standards that are widely accepted. The three key standards are SPF, DKIM, and DMARC; the third builds on and incorporates the previous two.
- Sender Policy Framework (SPF) – This email authentication is one of the newest ones, and it allows domain owners to decide which IPs can send emails on behalf of their domain. The email will only be delivered if a server matches one of the SPF’s allowed IP addresses.
- DomainKeys Identified Mail (DKIM) – This authentication standard uses key cryptography to sign an email message. This signature verifies that your message came from the right domain and wasn’t altered during the sending process.
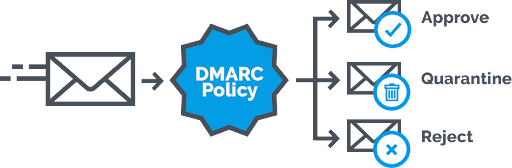
- Domain-based Message Authentication, Reporting, and Conformance (DMARC) – This email authentication policy and reporting protocol is one of the best for protecting email. If your domain is at DMARC enforcement, the domain in the From: field can be verified by the receiving domain, meaning that you can trust that the person who is sending that email is actually the right person. If the email is not authorized, the DMARC policy will reject or quarantine the message.
While these authentication standards are important, using just SPF or DKIM can still leave your domain vulnerable to phishing attacks. DMARC combines SPF and DKIM’s strengths while accounting for their weaknesses. For example, for an email to pass DMARC authentication, it must also pass either SPF or DKIM and align with the DMARC domain.
How does email authentication work?
Depending on the rules the owner of the sending domain has set up, the answers to this question can either validate a message (yes, it’s authentic, go ahead and deliver it!) or invalidate it (it’s not authentic–watch out!).
The rules include instructions for what the receiving server should do with non-authenticating messages, such as discarding them, putting them in a spam folder, or flagging them as potentially dangerous. Email authentication gives the domain owner global control of what happens to messages sent in their name by anyone, to anyone. It’s amazingly powerful and unlike any other kind of security tool.
What’s more, modern email authentication standards include a means for domain owners to get reports on who is using their domain names. In other words, if a company has authorized an email list provider, like MailChimp, to send messages on its behalf, it can see information about all emails sent by MailChimp’s servers and whether they authenticated adequately. They can also see all activity from scammers sending spam and phishing from unknown, unauthorized servers and “shadow email” services that may be legitimate but are not authorized.
Armed with this information, organizations can get a 360-degree view of their email ecosystem, a crucial requirement for having the confidence to enforce authentication globally.
Fortunately, email authentication eliminates the need to constantly monitor for and respond to alerts in real-time. Appropriately implemented, email authentication provides continuous protection and blocks anything that isn’t explicitly authorized. The reports tell the domain owner that a phishing attack was attempted – and failed.
Why do you need email authentication?
Why can’t you just look at an email and determine if it was sent from who it says it was? That’s because email headers, including the From: and Reply-to: fields, are remarkably easy to fake. In some cases, it’s as simple as typing:
“john@company.com”into the From: field.
Couple that with a legitimate-looking message and some persuasive graphics and formatting, and it’s entirely possible to fool people into thinking that a message in their inbox actually comes from their bank, the boss, or even the IRS.
This weakness in email has led to an uptick in phishing attacks aimed at getting employees or customers to click on malicious links, download and open malware-infested files, send W-2s and employee data to scammers, or wire funds into criminals’ accounts. The FBI estimates that business email compromise has cost businesses $50 billion in losses.
Strong email authentication protocols can protect your domain from these kinds of threats.
Check if your email is authenticating properly
To ensure your email authentication status works, try sending a test email from the domain you want to test. When you review the email, look for SPF, DKIM, and DMARC in the message header. You’ll be able to see the results of each protocol.
Pro tip: If you’d like an easier way to see if your domain is configured correctly, check out our free domain checker tool.
Uncover Email Security and Deliverability Issues
Challenges of email authentication
As you can see, for email authentication to work, it needs to be supported by both the originating domain (company.com) and the receiving email server (Gmail, Outlook.com, or your company’s email servers, for instance). The good news is that there is widespread support for email authentication standards.
Virtually every major provider of consumer and business email services, including Gmail, AOL, Microsoft, Yahoo, and more, supports email authentication, representing more than 5 billion mailboxes in all. The same is true for the major providers of email servers and secure email gateways (SEGs), and support is growing rapidly.
Despite the growing popularity, these protocols can still be challenging to implement. While you can get your domain to DMARC enforcement, it’ll take a lot of manual effort and time to keep it at enforcement. This is where automated DMARC can save the day.
