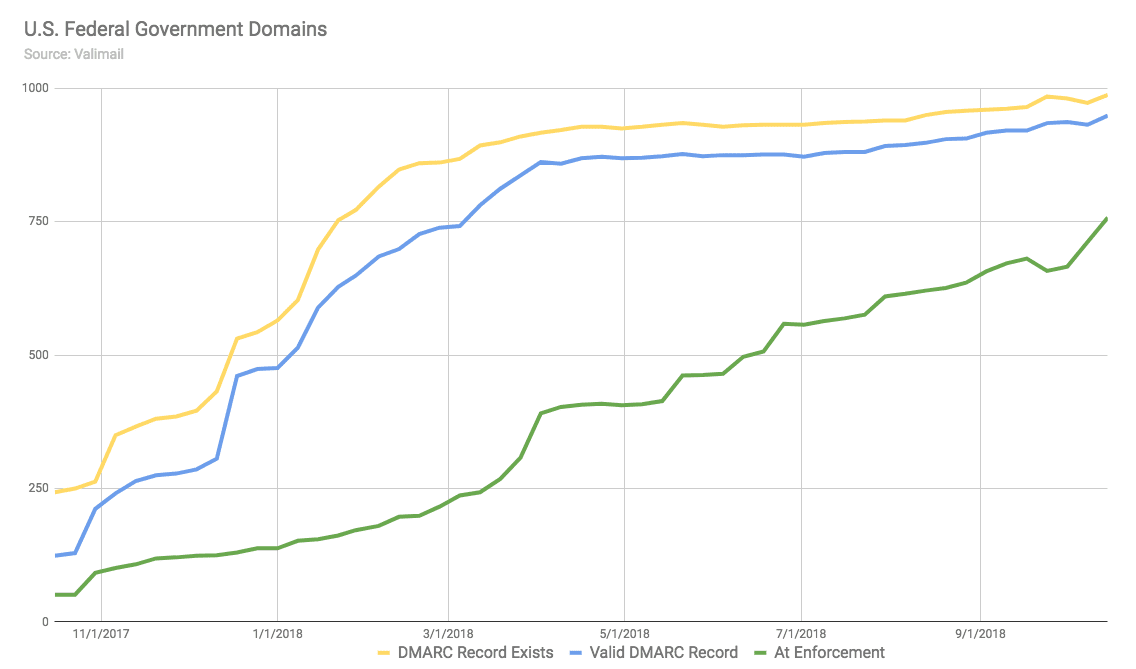
The deadline for compliance is past, but the number of federal domains protecting themselves against email impersonation continues to grow.
As of this week, 57 percent of all federal domains are protected by strict DMARC policies in compliance with government requirements. That’s a sharp jump from 50 percent at the beginning of the month — and we expect the number will continue to rise in the coming months.
The latest details are contained in Valimail’s updated report, “How Federal Agencies Are Meeting the Email Authentication Challenge,” which contains data current as of October 17.
Valimail has been tracking the DMARC status for 1,315 federal domains for the past year, ever since the Department of Homeland Security issued Binding Operational Directive 18-01 (BOD 18-01), which instructed most executive-branch agencies to deploy DMARC on all of their domains. The directive specified that all of these domains needed to have published DMARC records with a p=reject policy by October 16, 2018. This policy directs receiving mail gateways to delete any unauthorized mail that appears to be coming from the protected domain, and it is key to eliminating malicious spoofing of “From:” field addresses.
We saw a similar pattern in January, when the first major DMARC deadline hit. On January 15, the day by which federal agencies were expected to have DMARC records in place, we counted 698 domains with DMARC records (53 percent of the total), of which 589 were valid and correctly configured.
By mid-February, those numbers had risen to 848 (64 percent) and 699, respectively.
Today, there are 988 federal domains with DMARC records (75 percent of the total).
In other words, even though the January 15 deadline is long past, agencies continue deploying DMARC in order to come into compliance with it.
We expect that, having published a DMARC record, these agencies will now continue to gradually bring those domains into compliance with the October 16 deadline by moving their DMARC policies to p=reject.
This journey will be more challenging. Simply deploying a DMARC record at p=none carries no risk, but switching to a more restrictive policy does have a potential downside: If the domain owner has not correctly identified and authorized every sender that should be able to use the domain to send email, then moving to p=reject can result in mail gateways blocking legitimate (but not-yet-authorized) email messages.
But challenging does not mean impossible. (For example, 100% of Valimail’s federal customers reached BOD 18-01 compliance by the deadline, accomplishing their DMARC journeys in a median time of just three weeks.)
We have seen incredible progress in the past year, and the federal government has shown that DMARC is not only feasible, but carries broad benefits when adopted widely.
To learn more about how Valimail’s FedRAMP-authorized platform can help government domain owners identify senders and get to p=reject quickly, visit our government email authentication solutions page.