Ever get an email from “Amazon Support” and wonder if it’s actually Amazon? You’re not alone. With 89% of phishing attacks hiding behind fake identities, knowing how to verify an email sender is as important as learning how to lock a door.
In this guide, we’ll show you:
- Step-by-step tips for spotting fake senders
- How to check if an email sender is legitimate
- Ways to verify email addresses and sender domains
- Tools and techniques for email authentication
What is email sender identity?
Sender identity, aka who sent the email: Email sender information in the “From” field includes the sending domain name, email username, and sometimes the name of the person or generic account that the sender ties to this account, such as “John Smith” or “Amazon Tech Support.”
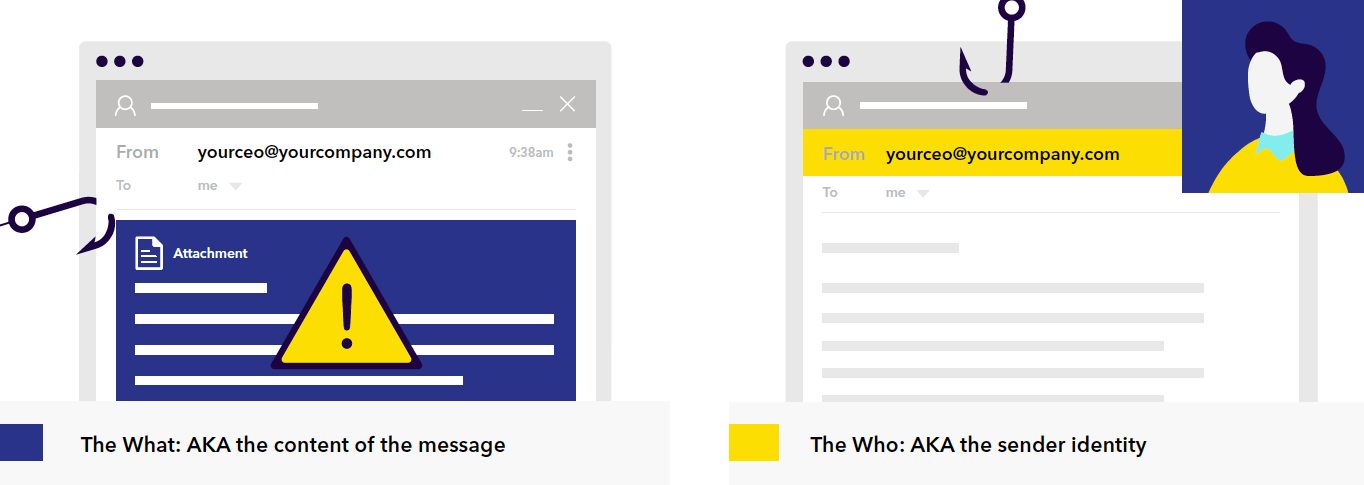
To date, the security industry has struggled to keep the lid on email fraud because it’s focused so heavily on understanding the content of email. But the more we double down on filters, link blacklisting, and other forms of content-based controls, the more the bad guys come up with new content variations that bypass these filters.
And yet, most companies are not putting enough focus on strong sender identity policies—despite the fact that deceptive identity is the primary technique used by phishers.
This mismatch between threat and response allows the majority of phishing attacks to reach users’ inboxes.
How to check if an email is legitimate
Before we dive into the technical stuff, here’s what you should look for when verifying an email sender:
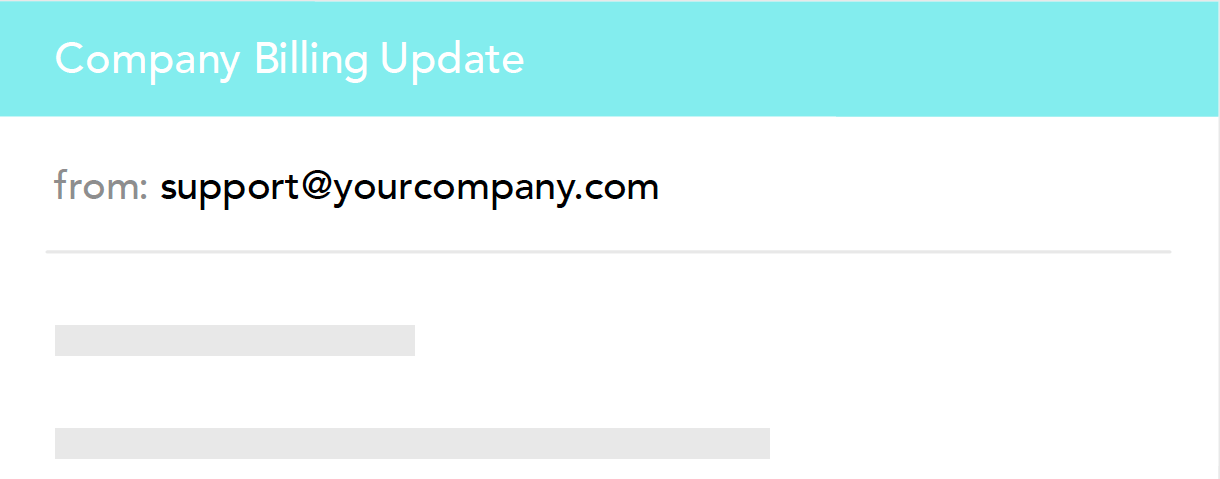
1. Check the actual email address, not just the display name
Ever notice how scammers love to use display names like “Amazon Support” or “Netflix Account Team”? Here’s the thing—anyone can make their display name look legitimate. The real truth lies in the actual email address.
Legitimate:
Suspicious:
2. Look at the sender domain closely
The domain (the part after the @) tells you a lot about who’s really sending the email. Scammers often use domains that look similar to legitimate ones, hoping you won’t notice the difference.
Legitimate domains:
- @netflix.com
- @amazon.com
- @microsoft.com
Suspicious domains:
- @netf1ix.com
- @arnaz0n.com
- @micros0ft-support.com
3. Check the email headers
Think of email headers as the DNA of your message—they tell you exactly where an email came from and how it got to you. Most email clients let you view these headers:
- Gmail: Click the three dots → “Show original”
- Outlook: Open email → File → Properties
- Apple Mail: View → Message → All Headers
Look for these key signs:
- “SPF: Pass”
- “DKIM: Pass”
- Matching “From” and “Return-Path” domains
How bad actors fake sender identity
It’s surprisingly easy for attackers to manipulate the identity of an email. There are three ways this can be done: exact-domain spoofing, lookalike domains, and open signups.
Exact-domain spoofing
With exact-domain spoofing, attackers appear as legitimate senders coming directly from the company’s own domain. In other words, they simply put an actual company email address in the “From” field of the phishing message. For most domains, this will be delivered in exactly the same way a legitimate message is, no matter where it was actually sent from.
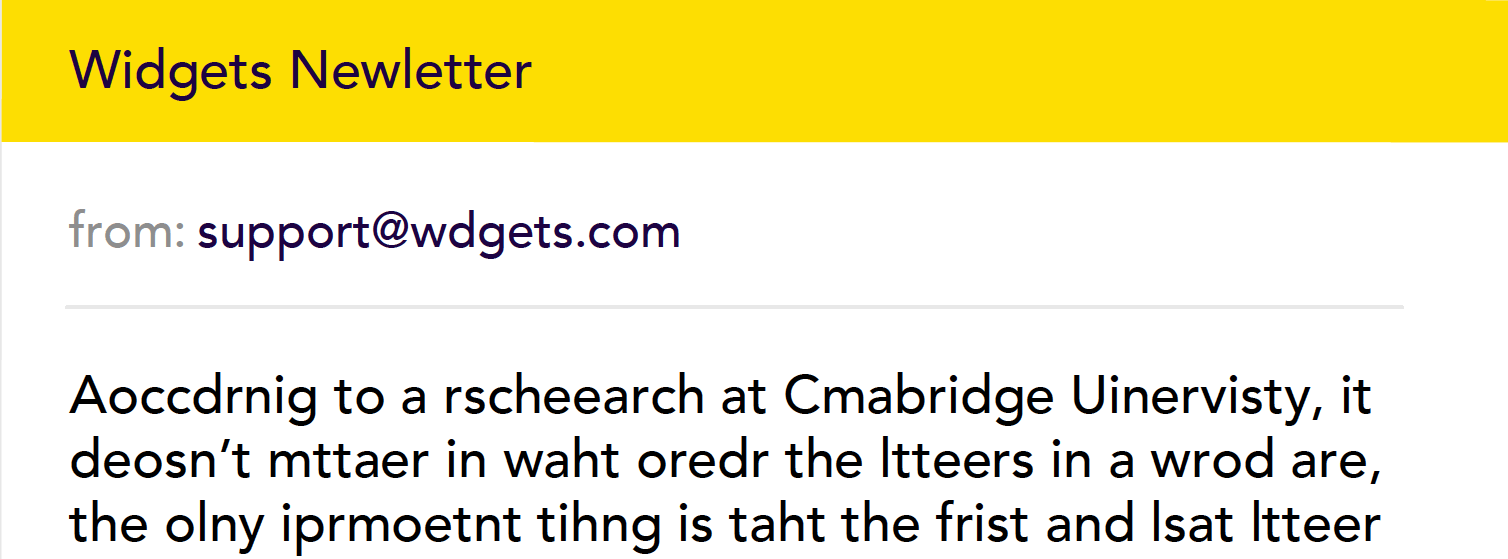
Lookalike domains
Attackers don’t necessarily have to spoof the exact domain to hit their target. Many use lookalike or cousin domains to get a “close enough” counterfeit of a brand or person’s email identity. For example, they may be able to trick plenty of users simply by registering something like w1dgets.com or wdgets.com to pass off as widgets.com.
This frequently works because of the way humans process information — filling in numbers and letters smoothly and unconsciously when they scan a word with missing or transposed letters.
Open signups that use a recognizable name
Another effective and simple method attackers use to fake sender identity is the open-signup attack. Also known as a “friendly-from” attack, this technique uses a generic email account on any number of trusted cloud email providers while assigning a “safe” looking fake display name to that address.
How to better verify email sender identity
1. Implement DMARC, SPF, and DKIM
- Domain-based Message Authentication, Reporting & Conformance (DMARC): DMARC guarantee that emails align with established policies and provides visibility into unauthorized use of your domain. By setting up DMARC, you can specify how your domain handles emails that fail SPF or DKIM checks.
- Sender Policy Framework (SPF): SPF allows domain owners to specify which IP addresses are allowed to send email on behalf of their domain. It helps prevent attackers from sending emails from unauthorized IP addresses.
- DomainKeys Identified Mail (DKIM): DKIM adds a digital signature to your emails, allowing recipients to verify that the email hasn’t been altered in transit and that it indeed comes from your domain.
2. Use advanced email filtering solutions
Deploy advanced email filtering solutions that leverage artificial intelligence and machine learning to analyze and identify suspicious patterns and anomalies in email sender information. These solutions can detect subtle variations and inconsistencies that might indicate a phishing attempt.
3. Regularly monitor DMARC reports
Regularly review DMARC aggregate reports (RUA) to gain insights into who is sending email on behalf of your domain. These reports can help you identify unauthorized senders and take corrective actions to mitigate the risk of email spoofing.
4. Use email authentication services
Consider using specialized email authentication services that provide comprehensive management and monitoring of your email authentication protocols. These services can help double-check that your SPF, DKIM, and DMARC records are correctly configured and enforced.
5. Conduct security audits
Perform regular security audits of your email infrastructure to identify and address vulnerabilities related to email sender identity. These audits should include a review of your email authentication practices and an assessment of your overall email security posture.
Common sender email verification challenges
Let’s break down some of the trickiest situations you might run into and how to handle them.
When perfect isn’t actually perfect
You get an email that looks exactly like one from your bank—same logo, same footer, even the same writing style. However, scammers have gotten really good at copying legitimate emails. Instead of just scanning for obvious red flags like bad grammar, you need to dig deeper. Hover over links without clicking them, check if images are actually embedded (not just linked), and pay attention to how they greet you. A bank that usually says “Hi [name]” probably wouldn’t switch to “Dear Sir” out of nowhere.
The multiple sender situation
Large companies like Amazon don’t just send emails from one domain. You might get messages from amazon.com, marketplace.amazon.com, or aws.amazon.com. This is totally normal, but it can make verification tricky. The key is making sure these domains follow a pattern—they should end with the company’s main domain. You can also check the company’s help center, which usually lists their official sending domains.
The urgency problem
Getting an urgent email from your boss asking for a wire transfer? This is where things get interesting. Business email compromise scams work because they play on our natural instinct to help, especially when it seems to come from someone we trust. If you get an unexpected request about money or sensitive data, take a breath. Call or message your boss through another channel—even if the email says it’s super urgent.
Those pesky account alerts
“Your account will be suspended!” “Unusual login detected!” Sound familiar? These alerts tap into our fear of losing access to important services. Instead of clicking email links, open your browser and log in to your account directly. If there’s really an issue, it’ll show up in your account notifications.
The attachment conundrum
Unexpected attachments are like mystery packages on your doorstep—even if they seem to come from someone you know, you need to be careful. Modern scammers have gotten clever with their tricks, disguising harmful files as innocent PDFs or making them password-protected to bypass security scans. If someone sends you an unexpected file, especially one that needs a password or claims to be a shared document, reach out to the sender through another channel first.
When tools disagree
Sometimes your email security tools might give you mixed signals about whether a sender is legitimate. When this happens, it’s better to err on the side of caution. Trust the more restrictive result, and if you’re still not sure, there’s nothing wrong with verifying through another channel. No legitimate company will ever fault you for being careful with your security.
Trust your instincts. If something feels off about an email—even if you can’t put your finger on exactly what—take the time to verify. Five minutes of double-checking beats dealing with the aftermath of a successful scam.
Verify sender identity with Valimail
Implementing strong email authentication measures like DMARC, SPF, and DKIM, and leveraging advanced filtering and monitoring solutions reduces the risk of fraudulent emails reaching your users.
Valimail is here to help. Our comprehensive email authentication solutions simplify the process of verifying sender identity to guarantee only legitimate emails reach your customers’ inboxes.
Sign up for a free demo today to learn how Valimail can protect your business, customers, and brand reputation.