DMARC enforcement is often discussed as a destination, but it is rarely explained as a journey. Many organizations understand that moving to p=reject is the only way to fully stop domain spoofing and impersonation attacks, yet they hesitate to take the first step. The fear is understandable. Enforcing DMARC without preparation can disrupt legitimate email, impact deliverability, and create internal alarm.
As a result, many teams remain stuck in monitoring mode for months or even years. They collect DMARC reports, see evidence of abuse, but never progress toward enforcement. This leaves domains exposed to spoofing while creating a false sense of security.
The reality is that DMARC enforcement does not require a leap of faith. It requires a phased, controlled approach that builds visibility, validates authentication, and reduces risk at every step. When implemented correctly, moving from p=none to p=reject is predictable, safe, and repeatable.
What DMARC enforcement actually means
DMARC enforcement defines how mailbox providers should treat email that fails authentication checks. It is controlled through the policy setting in your DMARC record, and it progresses through three distinct stages: monitoring, quarantine, and reject.
With p=none, DMARC is in visibility mode. Mailbox providers generate reports that show which messages pass or fail SPF and DKIM, but they do not take action on failing emails. This stage provides insight into sending behavior, but it does not stop spoofing or impersonation attacks.
With p=quarantine, mailbox providers begin taking action. Messages that fail DMARC are typically sent to the spam folder. This stage acts as a controlled testing phase, allowing organizations to confirm that legitimate email is properly authenticated while seeing how enforcement affects real-world delivery.
With p=reject, enforcement is complete. Messages that fail DMARC are rejected outright and never reach the recipient. This is the only DMARC state that fully prevents attackers from sending emails that appear to come from your domain.
Mailbox providers treat enforced domains differently. Domains with DMARC enforcement signal strong identity control and are less likely to be abused. Over time, this improves trust, protects brand reputation, and stabilizes deliverability.
Step one: Start with visibility using p=none
The first step toward DMARC enforcement is establishing visibility. This is done by publishing a DMARC record with a policy of p=none. At this stage, DMARC does not block or filter any email. Its sole purpose is to show you what is happening across your domain.
With p=none in place, mailbox providers begin sending aggregate DMARC reports. These reports reveal which systems are sending email on your behalf, whether those messages pass SPF and DKIM, and whether the authenticated domains align with the visible From address.
It is important to understand what p=none does not do. It does not stop spoofing. It does not protect your brand from impersonation. Visibility mode is a diagnostic phase, not a protection phase.
The goal of this step is to establish a baseline. You want to understand who is sending email for your domain, which senders are properly authenticated, and which ones are failing and why.
Step two: Identify all legitimate sending sources
Once visibility is established, the next step is identifying every legitimate service that sends email on behalf of your domain. This is where many DMARC projects slow down or stall, because email ecosystems are usually more complex than expected.
Legitimate senders typically include marketing platforms, CRM systems, customer support tools, billing systems, HR platforms, cloud applications, and internal mail servers. Subdomains are often used for different types of email, which adds another layer of complexity.
Shadow IT plays a major role at this stage. Teams may have adopted tools without informing IT or security, and those tools may be actively sending emails. DMARC reports often reveal senders that no one recognizes at first.
The objective of this step is to build a complete sender inventory. Every legitimate sender must be known and accounted for before enforcement can safely continue.
Step three: Authenticate every sender with SPF and DKIM
After all legitimate sending sources are identified, the next step is ensuring that each one is properly authenticated. DMARC depends on SPF and DKIM working correctly and aligning with the domain visible to recipients.
For SPF, this means authorizing every approved sending service in your domain’s SPF record. Care must be taken to avoid exceeding SPF lookup limits, which can cause legitimate messages to fail.
For DKIM, each sending platform should sign messages with a cryptographic key that aligns with your domain or an approved subdomain. DKIM is especially important because it scales better than SPF and is less fragile.
Alignment is critical. The domain authenticated by SPF or DKIM must match the domain shown in the From address. Messages that authenticate but do not align will still fail DMARC.
Step four: Validate and monitor authentication results
Once SPF and DKIM are configured, the focus shifts to validation. This step confirms that authentication is working correctly across real traffic.
DMARC reports should show pass rates increasing as issues are resolved. This phase also helps uncover false positives such as forwarding, mailing lists, low-volume systems, or legacy platforms.
The goal here is stability. Authentication results should be consistent and predictable across all major senders before moving toward enforcement.
Step five: Move to p=quarantine
After authentication results are stable, the next step is moving to p=quarantine. This introduces limited enforcement without immediately blocking email.
Mailbox providers begin diverting failing messages to spam folders. Legitimate, authenticated email continues to reach inboxes. This provides a real world test of enforcement behavior.
Quarantine is not the end goal. It is a validation checkpoint that confirms enforcement can be applied safely.
Step Six: Monitor and resolve residual issues
Even during quarantine, residual issues often remain. These are typically low volume senders, forgotten systems, or legacy platforms.
Each remaining failure should be investigated and either brought into compliance or intentionally retired. The objective is confidence that any remaining failures are acceptable to block.
Step seven: Implement p=reject for full protection
Once all legitimate senders are authenticated and residual issues are resolved, it is time to move to p=reject.
With reject enabled, mailbox providers block any message that fails DMARC. These messages never reach recipients. This fully shuts down domain spoofing and impersonation attacks.
At this stage, enforcement should feel uneventful. Legitimate email continues to flow normally. Only unauthorized or abusive messages are stopped.
Timeline expectations: Manual vs automated DMARC
Manually, most organizations take three to six months to reach p=reject, and many never complete the journey. Projects stall due to shadow IT, lack of ownership, or fear of disruption.
With automation, discovery and remediation happen faster. Many organizations can safely move to p=reject in two to four weeks. The key difference is confidence and visibility.
Common mistakes that delay DMARC enforcement
Common mistakes include staying in p=none indefinitely, incomplete sender discovery, overloaded SPF records, misaligned DKIM domains, and treating DMARC as a one time project instead of an ongoing control.
Avoiding these pitfalls keeps the roadmap moving and makes enforcement achievable.
How Valimail accelerates the path to reject
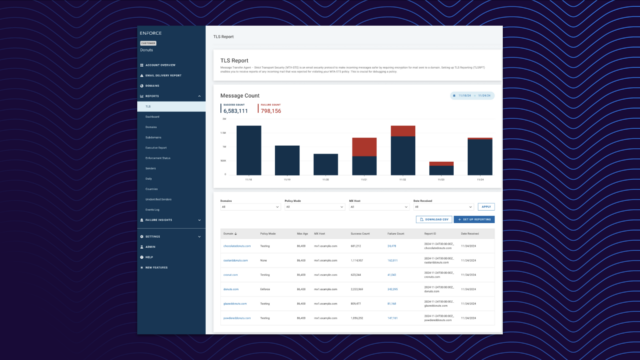
Valimail continuously discovers every service sending email on behalf of your domains. It monitors SPF, DKIM, and DMARC alignment in real time and surfaces issues as they arise.
Clear readiness indicators replace guesswork and show when it is safe to move from visibility to quarantine and from quarantine to reject. This compresses timelines and removes fear from enforcement.
Get to DMARC reject with Valimail
DMARC enforcement is not risky when approached correctly. Visibility enables control. Control enables enforcement. And p=reject delivers the protection DMARC was designed to provide.
With a phased approach and the right solutions, organizations can move from monitoring to full enforcement with confidence and permanently protect their domain from spoofing and impersonation.
FAQs about implementing DMARC enforcement
How do you implement DMARC enforcement step by step?
Start with p=none for visibility, identify all legitimate senders, configure SPF and DKIM for each source, validate alignment, move to p=quarantine to test enforcement, resolve residual issues, and finally enable p=reject.
How long does it take to move to p=reject?
Manually it often takes three to six months. With Valimail automation, many organizations reach reject safely in two to four weeks.
Why should you not start with p=reject?
Starting with reject without preparation can block legitimate email. DMARC is designed as a phased process to reduce risk.
What causes DMARC failures during enforcement?
Common causes include missing SPF entries, misconfigured DKIM, domain misalignment, shadow IT, and legacy systems.
Do you need both SPF and DKIM?
DMARC requires either SPF or DKIM to pass and align, but DKIM is strongly recommended for reliability and scale.
How do you know when you are ready for p=reject?
You are ready when all legitimate senders are identified, pass rates are consistently high, and remaining failures are understood and acceptable to block.
How does Valimail help?
Valimail provides continuous sender discovery, authentication monitoring, and clear readiness signals so organizations can enforce DMARC safely and confidently.