There’s a common misconception that simply using renowned mail services like Google or Microsoft guarantees comprehensive protection against email threats. While these giants offer robust support, the responsibility of implementing certain security measures (such as DMARC) largely falls on the domain owner.
This distinction between support and implementation isn’t just a matter of semantics—it’s the foundation of effective email authentication.
Many often ask, “If I use Google or Microsoft for my mail services, won’t they handle DMARC or email authentication for me?” The short answer is that they provide support, but they don’t implement it.
Below, we’ll dive deeper into what Office 365 and G Suite do for your email security and how to ensure you have the comprehensive DMARC coverage your business needs.
DMARC Office 365 and G Suite
So, you already use Google or Microsoft to run your mail services. Can’t they just take care of DMARC or email authentication for you?
Good question. The shortest answer is no, not quite. But let’s dig a bit deeper.
Short answer:
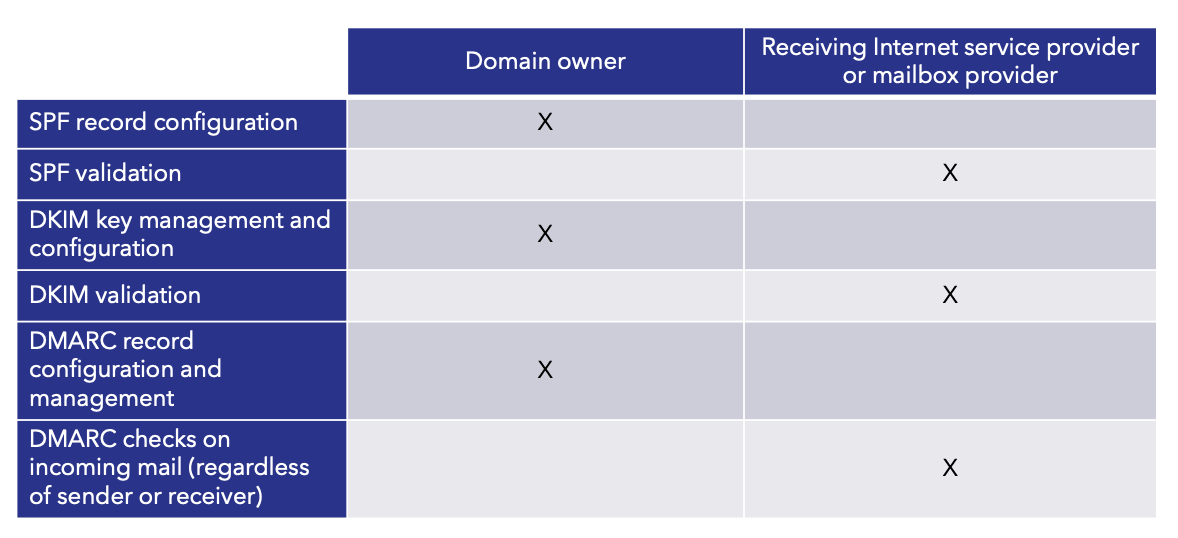
They support, but they don’t implement. The distinction is important because for email authentication to work, both senders and receivers need to play a part.
Fortunately, 100% of U.S.-based email receivers provide support for DMARC authentication on inbound email. In fact, inbox providers like Gmail and Yahoo are starting to require DMARC for senders to keep sending.
However, they can only do DMARC authentication for domains that have published (implemented) DMARC records.
Internet/Mailbox service providers alone cannot remove the implementation burden for email authentication.
The little bit longer (but still short) answer:
Google, Microsoft, and all U.S.-based Internet/Mailbox service providers, as well as 80% of email receivers worldwide, support DMARC by running authentication checks when receiving email. Unlike some SEGs, which require DMARC validation, G Suite and O365 do DMARC validation out of the box.
However, it is up to the owner of the sending domain to publish the correct SPF, DKIM, and DMARC policies in DNS. Without setting those policies, email receivers—including G Suite and Office 365—will not have the information needed to determine whether an email is authenticated. Nor will they be able to block spoofed messages that appear to come from that domain.
Receiving mail systems rely on DNS to authenticate messages. When an email is received, they will run validations utilizing the DKIM key, SPF record, and DMARC record published in DNS — if those exist for the sending domain. If a domain owner hasn’t provided this information to the receivers, no action can be taken.
In other words, they will validate a policy, but only the domain owner can specify that policy.
That includes your own domain. To protect yourself from spoofing, you need to enable DMARC checks for inbound mail — and configure SPF, DKIM, and DMARC for your domain to protect all email sent as you.
This is what is meant by “implementing DMARC.”
Do you have DMARC policies implemented for your domain? Use our domain checker to find your DMARC status.
DMARC Is Global and More Than Just Incoming Mail
What makes DMARC so powerful is that it protects your domain — globally. While secure email gateways and Internet/Mailbox providers provide additional benefits for organizations that use them, only email being sent to your organization is visible by these technologies.
DMARC extends beyond just your service provider and provides a mechanism for any receiver to get the information they need to determine the authentication status of the email it has received. What’s more, DMARC provides you (the domain owner) with visibility into all email being sent using your domain.
Once you’ve implemented DMARC and achieved DMARC enforcement on your domain, it will protect you against inbound and outbound impersonation. Inbound impersonations are aimed at fooling employees into thinking they’re receiving an email from an executive or colleague, like an email that appears to come from yourceo@yourdomain.com asking you to wire funds.
DMARC at enforcement also protects your domain from being abused outside of your walls, or what is sometimes called “outbound” impersonation. This could be fraudulent emails from support @yourdomain.com asking your customers to update their billing info, or an email from yourcfo@yourdomain.com to one of your partners telling them that “your company” has a new deposit account.
Here’s a quick guide for understanding the different roles of your business and those of a service provider when it comes to email authentication:
Automate DMARC With Valimail Enforce
Navigating the nuances of email authentication can be daunting, especially when the stakes are as high as safeguarding your brand’s reputation and customers. While understanding the differences between support and implementation is important, the process of setting up and maintaining DMARC can be time-consuming and complex.
Fortunately, we can help.

We built Valimail Enforce to simplify the DMARC process. Valimail Enforce provides an automated solution that takes the guesswork out of DMARC implementation. Instead of manually configuring and monitoring DMARC records, Valimail Enforce streamlines the process and guarantees your email authentication setup is correct and optimized for maximum protection against impersonation and phishing attacks.