Subdomain takeover: What it is and how to prevent it

Learn everything you need to know about subdomain takeover and how to protect your business from cybercriminals.
Accelerating visibility: Monitor vs. Enforce in the ultimate email race

Explore how Valimail Monitor and Enforce race for email sender visibility, speeding up your path to clarity, security, and brand protection.
Why switching to Valimail is the apparent choice for DMARC management
Switching to Valimail transforms DMARC management with faster setup, cost savings, and support. Discover why Valimail is the ultimate email security solution.
DMARC growth in 2024: A snapshot of surging adoption
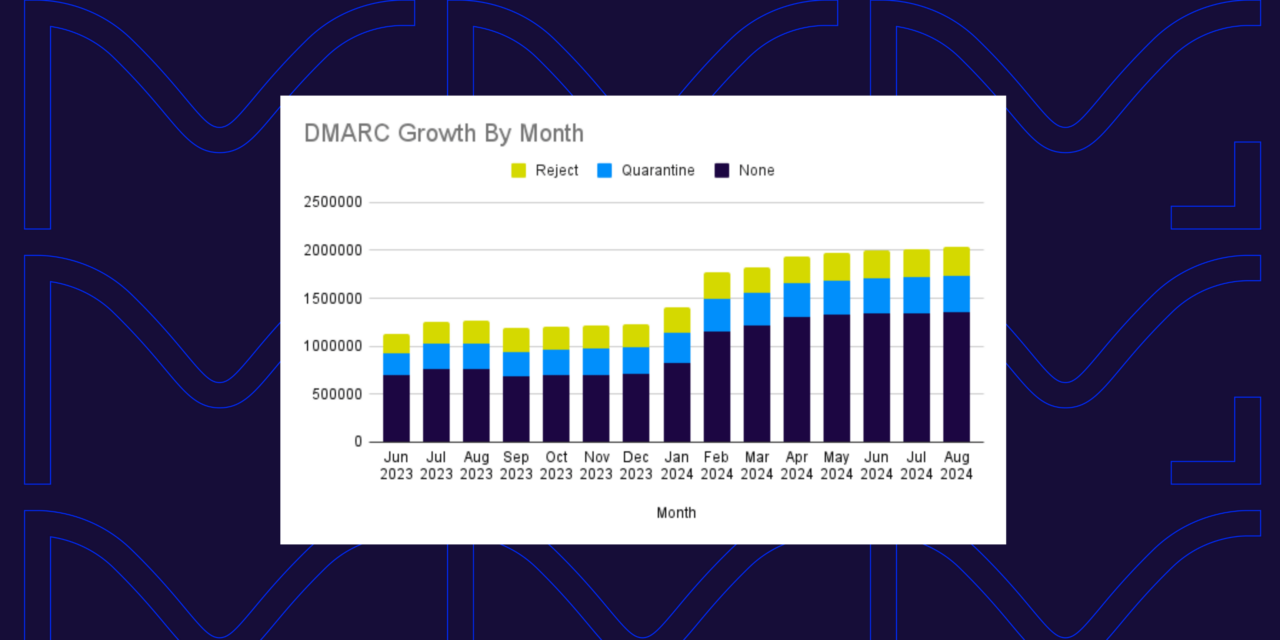
Explore the latest trends in DMARC adoption in 2024. Discover how the top domains are implementing DMARC to combat phishing in this snapshot of rapid growth.
Multiple SPF records (and what to do about it)

We’ll walk you through everything you need to know to identify and resolve multiple SPF records—and we’ll also show you how to automate the process.
Can you protect yourself from being scammed? How to spot fake emails

Think you can spot a scam? Learn how to protect yourself by identifying fake emails through red flags that signal a phishing attempt. Stay secure with these expert tips.
DMARC policies: How to know when to move from p=none to p=reject
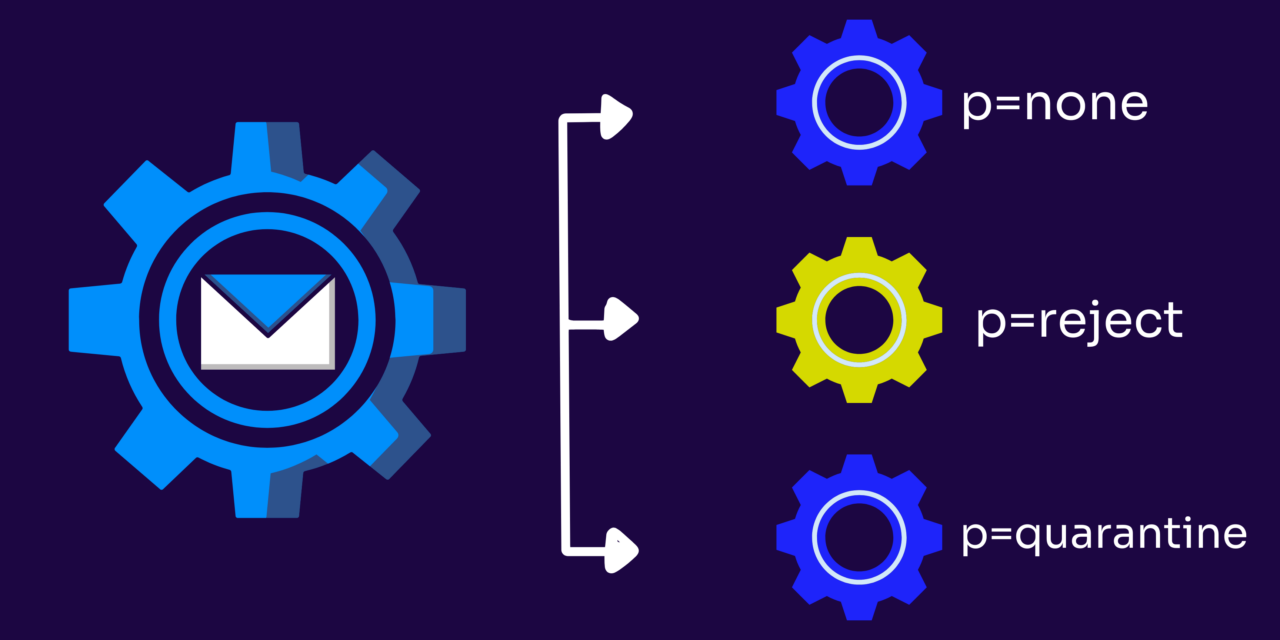
Learn when and how to move your DMARC policy from p=none to p=reject to boost email security, protect your brand, and increase customer trust.
DMARC in higher education: Securing university email systems

Learn the importance of DMARC for universities, the challenges they face implementing it, and the impact of neglecting this non-negotiable security measure.
DMARC international coverage grows with DMARC reports from 1&1

1&1, a leading German global web hosting and internet service provider is now sending DMARC report feedback. Get the latest here.
DMARC and third-party senders: How to navigate them
Learn the two main scenarios that could complicate your DMARC process when working with third-party senders and what to do about it.
DKIM l=tag vulnerability: Working to mitigate the threat
Curious on how the DKIM l=tag vulnerability is affecting email months after being brought to light? Check out the latest here.
Secure email gateways (SEGs) and email authentication: Why you need both
Learn how to use Secure Email Gateways (SEGs) and email authentication to give your brand the complete protection it needs against email threats.