It just keeps happening. A prankster who over the past few months tricked the heads of several major banks into thinking that they were having email conversations with their colleagues has struck again, this time targeting members of the Trump administration.
Former communications director Anthony Scaramucci fell for the trick, just days before the end of his short-lived tenure: The prankster posed as Reince Priebus in emails that poked fun at Scaramucci’s pay and his spelling. Scaramucci was irritated enough to fire back in an email to the supposed Priebus, which the prankster promptly published on Twitter.
Homeland security advisor and White House cybersecurity expert Tom Bossert fell for prank emails sent from an account that looked like Jared Kushner’s, and even responded to the prankster with his personal email address — and this despite the fact that his email system flagged the prankster’s mail as likely to be spam.
The prankster also ensnared Eric Trump (who is not an official member of the administration) by posing as his brother, Donald Trump.
What can we learn from this mostly harmless (but embarrassing) episode?
Emails are way too easy to fake.
By default, Internet email includes no provisions to guarantee the authenticity of the person or email address shown in the “From” field of a message. As a result, it’s very easy for hackers and phishers to put bogus information in that field. In this case, all the prankster had to do was create a throwaway Mail.com account and enter “Reince Priebus” as the “Friendly From” name. If he had been somewhat technical, it would have been easy for him to take the additional step of putting an address like “reince.priebus@whitehouse.gov” into the From field, making the message nearly indistinguishable from a legitimate message.
People are quick to respond to people they believe are friends and associates.
Think about it: If you see an email in your inbox from a coworker or a friend, and there’s even a small amount of urgency about the message, your first instinct is probably to start composing a reply. Skillful phishers (and pranksters) capitalize on this instinct by crafting messages that are chatty, friendly, and have an element of urgency or immediacy to them. “Phishing impersonation, like this example of email pranking, once accomplished, is leverage to the next steps of attack,” writes Violet Blue on Engadget. ” In this instance, it was pretty easy to get those doors open and get the targets talking.”
It’s really, really hard to train people to be suspicious of phishing emails.
Study after study has shown that people readily respond to well-crafted inbound emails, or download attachments, even if they have been trained on how to identify phishing attempts.
We need better systems for authenticating email and for flagging non-authenticated (untrusted) messages.
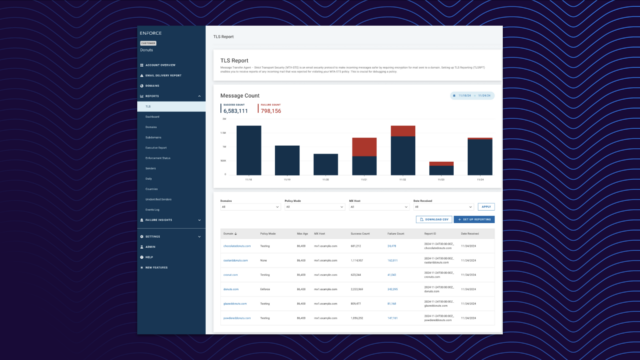
One part of the solution is here already: email authentication through the DMARC (Domain-based Message Authentication, Reporting & Conformance) standard ensures, for any emails you receive, that the address in the From field is legitimate. DMARC works with over 2.7 billion email inboxes already, including the vast majority of major consumer and enterprise email providers, such as Google, Microsoft, AOL, Yahoo, and others.
It is true that DMARC would have done nothing to prevent this prankster’s emails from getting through. The only thing he faked was the Friendly From address, leaving obviously wrong Gmail addresses in the From field. And given that Bossert replied to the prankster’s message despite a prominent “SUSPECTED SPAM” warning, it’s clear that human fallibility will always be a weak link.
However, wider acceptance of DMARC would make it easier for email service providers and email clients alike to implement a wider range of protective measures. For example, Google has started to do this, with a question mark that appears next to email messages that fail SPF or DKIM, adding warnings about suspicious “lookalike” domains, and other measures.
On the sender side, DMARC usage by domain owners is relatively small, but growing exponentially. (It is not used by whitehouse.gov, however, as Valimail’s free domain analyzer shows.) As it becomes more ubiquitous, we will need ways to make it clear to recipients which emails are authenticated and which aren’t.
After all, if people at the White House are ignoring spam flags to reply to bogus messages, it’s clear we need better tools to help people recognize trusted emails and differentiate them from untrusted emails.