DMARC adoption momentum builds in Japan in 2024
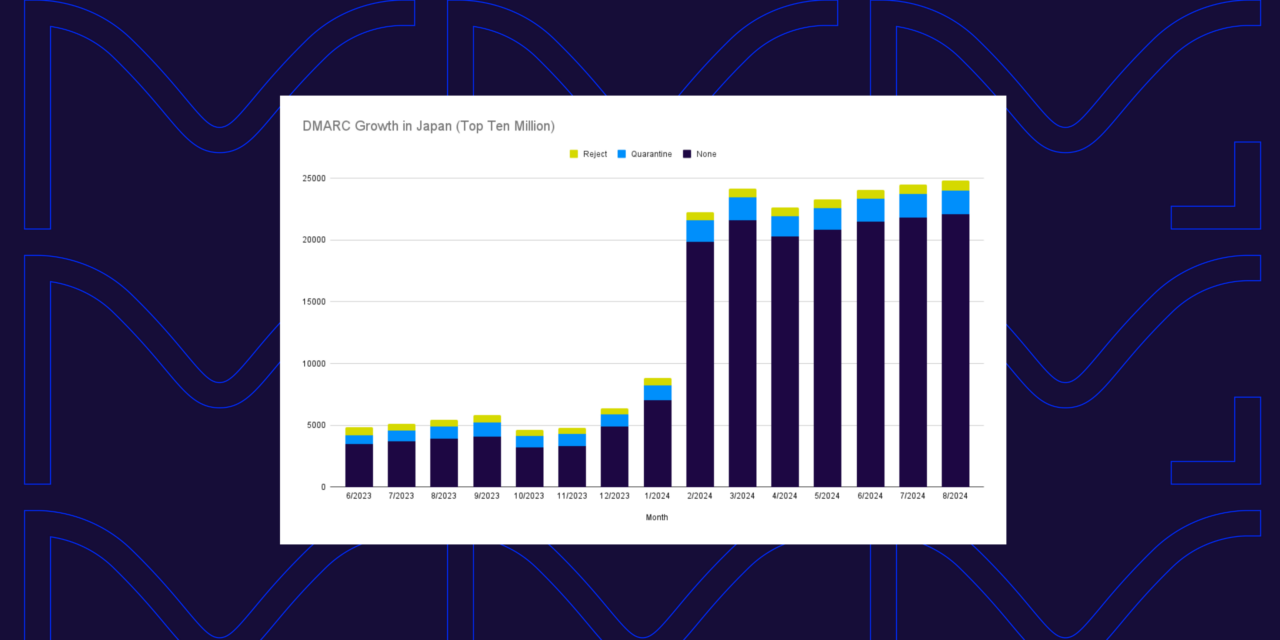
Explore 2024 DMARC adoption trends among Japan’s .jp domains, the impact of new sender requirements, BIMI growth, and how to improve email security beyond p=none.
DMARC growth in 2024: A snapshot of surging adoption
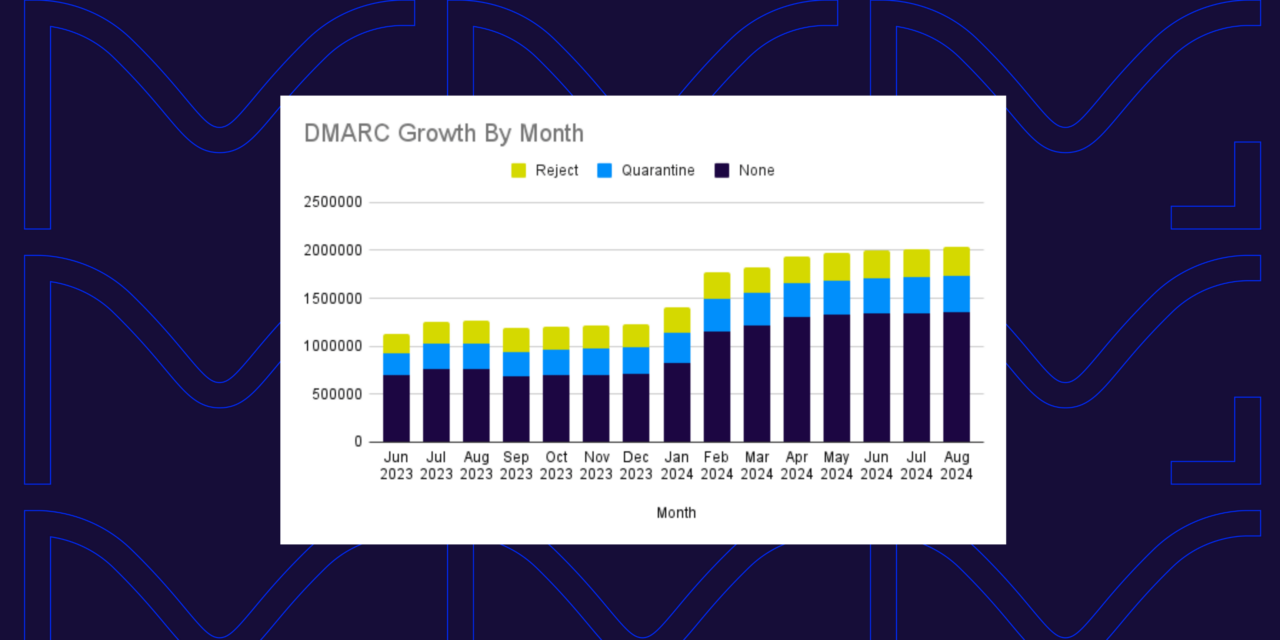
Explore the latest trends in DMARC adoption in 2024. Discover how the top domains are implementing DMARC to combat phishing in this snapshot of rapid growth.
DMARC in healthcare: Securing email for hospitals and clinics
Learn how DMARC can secure your healthcare organization’s email program and how to get started.
Multiple SPF records (and what to do about it)

We’ll walk you through everything you need to know to identify and resolve multiple SPF records—and we’ll also show you how to automate the process.
Can you protect yourself from being scammed? How to spot fake emails

Think you can spot a scam? Learn how to protect yourself by identifying fake emails through red flags that signal a phishing attempt. Stay secure with these expert tips.
DMARC policies: How to know when to move from p=none to p=reject
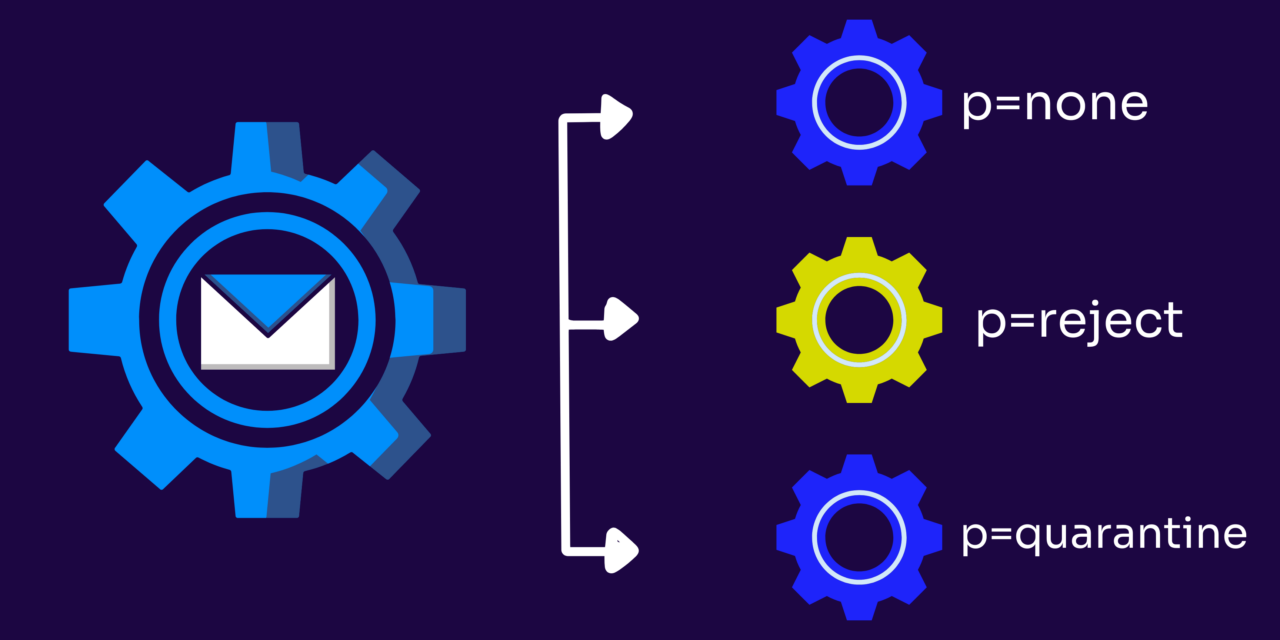
Learn when and how to move your DMARC policy from p=none to p=reject to boost email security, protect your brand, and increase customer trust.
SPF record limitations: Why it’s not a stand-alone solution

Learn all about the limitations of SPF records and how they’re an incomplete solution unless you also implement DMARC authentication.
Proofpoint email routing exploit: What you need to know

Bad actors were able to exploit a common configuration setting in Proofpoint’s email relay service to send millions of spoofed email messages.
DKIM l=tag vulnerability: Working to mitigate the threat
Curious on how the DKIM l=tag vulnerability is affecting email months after being brought to light? Check out the latest here.
Webinar recap: Enhancing email deliverability in political campaigns
Did you miss our webinar with NGP VAN? Read the recap to get tips from industry experts on how to help improve your deliverability.
Mailing lists and authentication: How they work with ARC
Learn how Authenticated Received Chain (ARC) fixes the problem between mailing lists and email authentication protocols.
Email Cybersecurity vs. Email Authentication: What’s the Difference?

Learn about the differences and similarities between email cybersecurity and email authentication to ensure you have the end-to-end protection your business needs.