On May 2, 2024, The Federal Bureau of Investigation (FBI), the US Department of State, and the National Security Agency (NSA) issued a Joint Cybersecurity Advisory warning of North Korea’s attempts to exploit improperly configured Domain-based Message Authentication, Reporting & Conformance (DMARC) record policies to conceal email-based social engineering attempts.
In the report, this group of US government agencies warns (and shares examples) of phishing email messages sent by North Korean cyber actors between late 2023 and early 2024. They include examples of spoofed message bodies and email message headers to demonstrate examples of the attacks.
Are you at risk?
Today, North Korea is specifically targeting journalists, academics, and other experts in East Asian affairs, looking to compile covert intelligence on things affecting North Korean interests. Even if this is not your area of expertise or if it doesn’t relate to your field of business, remember that if you’re similarly vulnerable, other bad actors with other targets are likely to come along and look to obtain access (and cause damage) to your network, systems or data, utilizing similar exploits.
There is nothing about these types of phishing attacks that inherently limit themselves to certain regions or government-related entities.
Is your domain at risk? Use our free domain checker to see your DMARC status and ensure you’re protected.
What the hackers are actually doing
Knowing that DMARC helps restrict who can successfully send spoofed email as a given domain, these bad actors seem to be hunting for two things in particular:
- Domains lacking any sort of DMARC implementation mean the domain has not established a DMARC record in DNS or that the DMARC record is malformed.
- Domains with a DMARC policy that does not protect against spoofing (in other words, a p=none DMARC policy), meaning a domain does indeed have a DMARC record in place, but the policy specified in that record is not configured properly to prevent successful phishing and spoofing.
It’s very easy for bad guys to collect the DMARC policy for different domains, and it’s safe to assume that they’re looking through that universe of domains, searching for unprotected ones that could represent targets valuable enough to make them useful for phishing attacks.
After these bad actors identify imperfectly protected domains, they send spearphishing emails directly targeting employees of affected organizations. They often attempt to trick a recipient into installing malware or giving up sensitive personal or business-related information.
Domain owners are at risk if they have yet to implement DMARC for their domains or if that policy is p=none. It is important to note that with the recent Yahoo and Google sender requirement updates, many domain owners quickly implemented a p=none DMARC policy, assuming that this was “good enough” to comply. (While it satisfies current inbox provider requirements, it does not properly secure your domain against phishing or spoofing.)
DMARC policy and why it matters
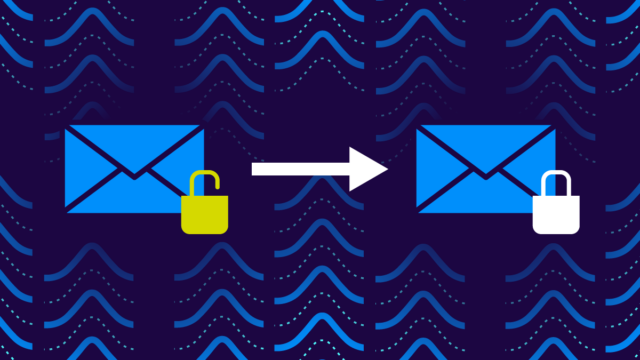
When discussing DMARC, it’s essential to understand the different policies domain owners can specify and how they relate to enforcement and protection against phishing and spoofing.
DMARC has three possible policy settings:
- p=none: Publishing a policy of none (p=none) means you’re asking Inbox providers to take no action (such as filtering or blocking) when they encounter an inbound email message that fails authentication checks.
- p=quarantine: Publishing a quarantine policy (p=quarantine) means you’re asking inbox providers to route inbound email messages that fail authentication checks to a spam, junk, or quarantine folder.
- p=reject: The most restrictive option, publishing a policy of reject (p=reject), means that you are asking inbox providers to reject any inbound email message that fails authentication checks.

Which makes the most sense for you can vary – learn more here, but you can’t consider a domain secured unless the policy is set to quarantine or reject. A policy of none offers no protection at all.
How you can protect yourself
More than 1.3 million of the top 10 million domains (from our April 2024 data snapshot) have implemented DMARC with a p=none policy. This is a common first step when implementing DMARC (with, for example, Valimail Monitor) to help monitor and understand all of the different sources of email that are sent using your domain name. But it’s important to remember that p=none can’t be the final step; otherwise, your domain is not secure.
Ultimately, the goal should be to implement DMARC and move to DMARC enforcement by way of a p=quarantine or p=reject policy.
The whole path from start to finish can be tricky if you’re doing it on your own. We have a step-by-step guide of everything you need to think about along your DMARC process, but more importantly, we’ve got the tools and expertise to help you through this journey.
Need help getting to p=reject or quarantine?

Al Iverson is Valimail’s Industry Research and Community Engagement Lead, bringing over 25 years of experience in email marketing, technology, and deliverability. He’s committed to helping people learn more about DMARC and adopt it beyond just the minimum requirements while also helping good people send email and get their mail delivered.