3 types of dangerous email impersonation attacks to beware
Learn everything you need to know about the latest email impersonation attacks to better protect your business, employees, and customers.
DMARC benefits: What’s the real value of DMARC?

Discover all the DMARC benefits and how DMARC at enforcement can be a game-changer for your business’s email communications, brand, and customer protection.
Email Authentication and Protection with Valimail and .BANK
Valimail and .BANK partner together to provide your bank the best protection against phishing and BEC attacks.
Webinar Recap: Valimail + Abnormal = Better Together
Did you miss Valimail and Abnormal’s webinar? Read on to catch up on the highlights.
How to Avoid Tax Phishing Scams This Season
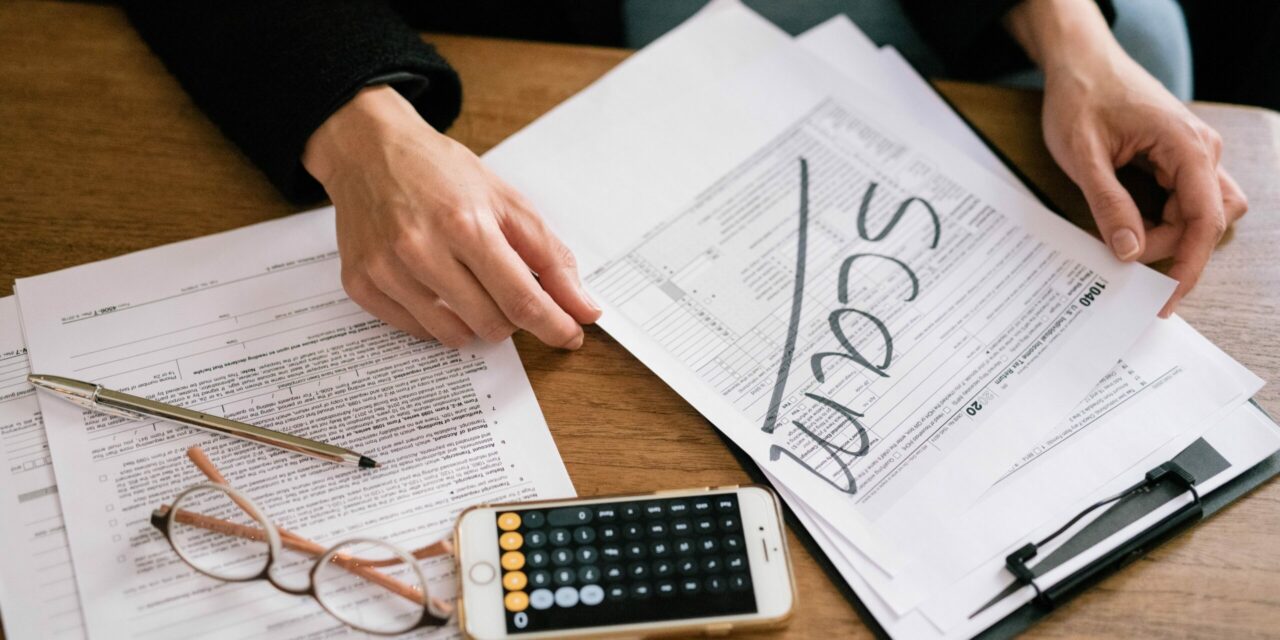
Avoid tax phishing scams this season with these tips.
DMARC tags: The only 3 tags you really need (RUA, P, & V)

Have you heard of DMARC tags? There are three main ones: rua, p, and v. Learn more about these tags and how they can help you.
CISOs want measurable results, survey shows

CISOs want measurable results, survey shows Enterprises tend to spend a lot on cybersecurity. So you’d think they’d be insisting on — and getting — measurable results. It’s not necessarily so. According to a survey of almost 300 IT security executives conducted by SC Media and research firm C.A. Walker, cybersecurity vendors often fail to […]
CEO to CFO phishing scams are on the rise. Here’s one we caught in the act
There has been a lot of coverage in the media recently about spear phishing and the ‘CEO to CFO’ scam, and for good reason. Phishing attacks have been distressingly common for some time, and they appear to be getting worse. For a sampler, just check out security expert Brian Krebs’ many stories of executives being duped by fake emails. […]
Email Impersonation Knows No Borders
Hello…Elvis? Photo credit: Gunnshots Email impersonation scams, also known as business email compromise (BEC) or phishing attacks, have risen 20 percent in the first nine months of this year, according to the Singapore police. According to the report, those scams have cost Singaporeans S$19 million (U.S. $13.4 million), of which the police have only been […]
One of Europe’s biggest companies just lost $45M in a business email scam
Leoni AG, a billion-dollar (market cap) manufacturer of cables and cable harnesses for car manufacturers, announced last month that it had fallen victim to a business email compromise (BEC) scam. The cost? 40 million Euros, or about $45 million. Leoni announced the fraud on August 16, a few days after it had happened. Upon hearing the news, the […]
Senior Execs Fired for Spear Phishing Success

In the wake of the much-discussed payroll company that fired an employee for falling victim to a spear phishing scam, an Austrian manufacturer has fired its CEO and financial chief after the company gave away more than $50 million due to a CEO impersonation attack. As with Alpha Payroll, it’s worth asking: Did the company, FACC AG, take the […]
A Better Way to Respond to Phishing Attacks
An employee at payroll service provider Alpha Payroll got fired for falling victim to a phishing scam, as CSO Magazine’s Steve Ragan reported recently. You can read about it at the above link, but the brief recap is that in response to a breach, payroll service provider Alpha Payroll informed the New Hampshire attorney general of the breach […]